Medium
2w
82
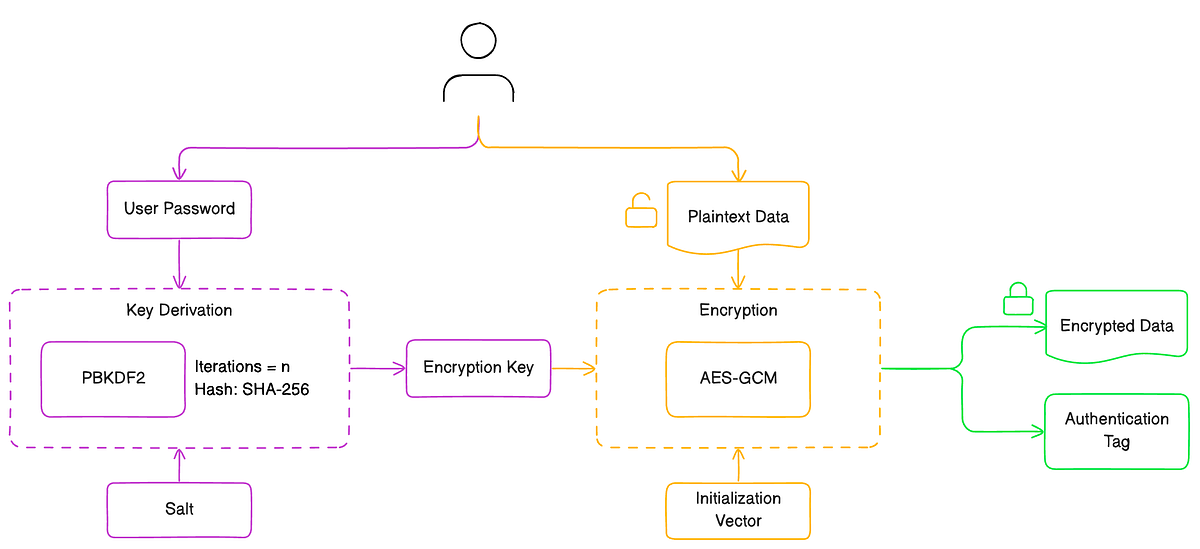
Image Credit: Medium
How to secure encrypt and decrypt data within the browser with AES-GCM and PBKDF2
- Directly using user passwords as encryption keys is not advisable due to their predictability and vulnerability to being guessed or cracked through brute-force attacks.
- The secure cryptographic key generation starts with the user’s password, processed through the PBKDF2 algorithm using SHA-256 hashing.
- When it comes to encrypting data with AES-GCM, there are essential steps to follow, including generating an IV and transforming plaintext data into ciphertext.
- The decryption process reverses the encryption steps, using the same key, IV, and authentication tag to ensure the data’s integrity has not been compromised.
Read Full Article
4 Likes
For uninterrupted reading, download the app