Medium
1w
264
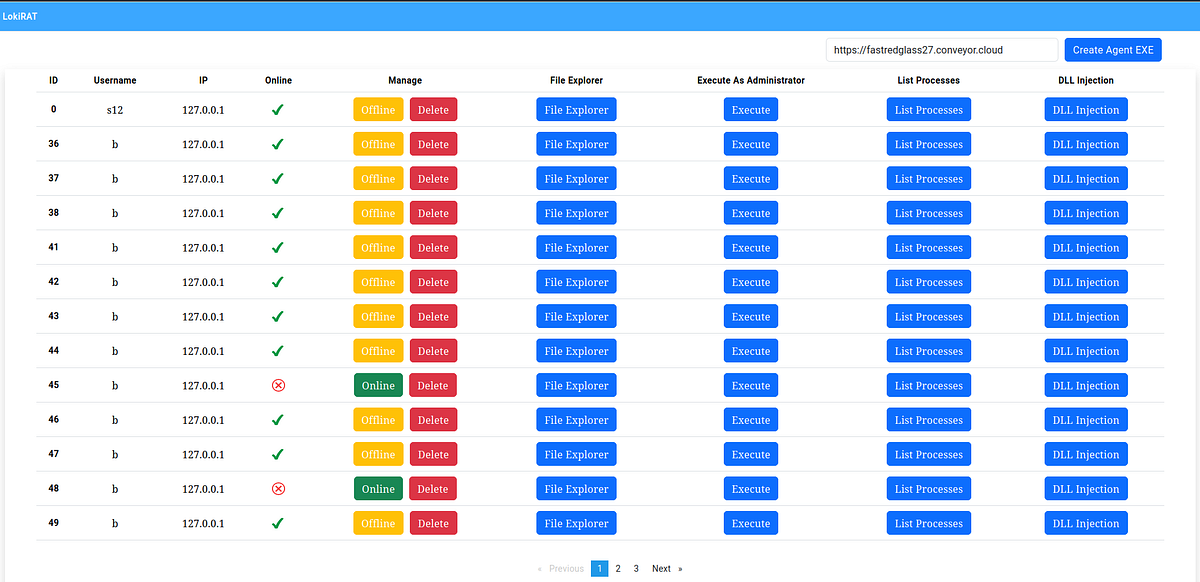
Image Credit: Medium
DLL Injection in Web RAT
- The article explores DLL injection techniques within a web-based Remote Access Trojan (RAT) system.
- It explains the process of initiating DLL injection requests, specifying the target process name and the DLL path.
- The article also discusses the server-side implementation using C#, error handling, and parameterized SQL queries.
- Additionally, it provides insights into the C++ code responsible for DLL injection on the victim's machine.
Read Full Article
15 Likes
For uninterrupted reading, download the app