Securityaffairs
1M
239
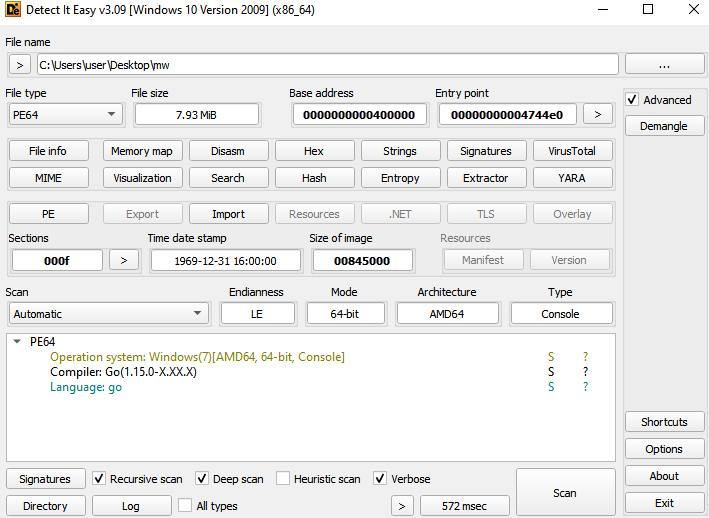
Image Credit: Securityaffairs
New Golang-based backdoor relies on Telegram for C2 communication
- Netskope Threat Labs discovered a Golang-based backdoor using Telegram for C2 communication, believed to be of Russian origin.
- The backdoor exploits cloud apps to evade detection and acts as a backdoor after execution.
- The malware connects to Telegram using an open-source Go package and supports four commands, including executing PowerShell commands and self-destruction.
- The use of cloud apps presents challenges to defenders, and this backdoor highlights the utilization of such apps by attackers.
Read Full Article
14 Likes
For uninterrupted reading, download the app