Cyber Security News
Tech Radar
88

Image Credit: Tech Radar
International Criminal Court says it was hit by sophisticated cyberattack
- The International Criminal Court (ICC) has confirmed a recent cyberattack described as 'new, sophisticated, and targeted' which has been contained and is being mitigated.
- No responsible threat actors have been identified yet, and the details of the attack, including any consequences, have not been disclosed.
- The ICC operates independently from the United Nations and focuses on prosecuting individuals for serious international crimes, with recent media reports linking the cyberattack to the indictment of Israeli PM Benjamin Netanyahu for alleged war crimes in Gaza.
- Given the history of the ICC being targeted and its controversial cases, such as the indictment of Netanyahu, tightening security measures is being emphasized to prevent potential future cyberattacks.
Read Full Article
5 Likes
Kaspersky
264

Image Credit: Kaspersky
The top-five funny school, social media, and IoT hacks | Kaspersky official blog
- Hacks include prank traffic lights, classroom Rickroll, robot vacuums, Lenovo website, Twitter pranks.
- Hackers targeted traffic lights with Zuckerberg and Musk voices, students performed classroom Rickroll.
- Ecovacs robot vacuums hacked, Lenovo website defaced, Twitter accounts hijacked for pranks.
- Lessons learned: avoid weak passwords, use strong, unique passwords for online security.
Read Full Article
15 Likes
TechJuice
168

Image Credit: TechJuice
NCCIA Shuts Down 12 Illegal Call Centres Under ‘Operation Grey’
- The National Cyber Crime Investigation Agency (NCCIA) conducted Operation Grey, targeting cyber scams and digital money laundering by shutting down 12 illegal call centres and arresting over 90 suspects, including foreign nationals.
- The operation aimed to dismantle networks involved in online fraud and unauthorized international financial transfers, with these illegal call centres orchestrating large-scale scams globally.
- 93 individuals were apprehended, including foreign nationals and key Pakistani facilitators, linked to fraudulent schemes siphoning profits out of Pakistan through international digital channels.
- NCCIA reiterated its strong stance against cybercrime, with further actions planned to track additional accomplices and financial conduits associated with these illegal networks.
Read Full Article
10 Likes
Tech Radar
46

Image Credit: Tech Radar
Swiss government warns data stolen in third-party ransomware attack
- Swiss government files were stolen and posted on the dark web following a ransomware attack on Radix, a third-party supplier.
- Radix, a non-profit organization in the health promotion sector, notified the National Cyber Security Centre of the breach in which various administrative units of the Swiss federal government were affected.
- Despite the attack, Radix claims that all data is intact on backups and no direct access to Federal Administration systems was gained by the attackers.
- The incident involving the ransomware group Sarcoma has led to an investigation to determine the extent of the data breach, but Radix states that partner organizations' data remained uncompromised.
Read Full Article
2 Likes
Siliconangle
117

Image Credit: Siliconangle
Exabeam expands Nova AI platform with new strategy agent for CISOs
- Exabeam Inc. expands its Nova AI platform with a new cybersecurity strategy agent for CISOs.
- The Nova Advisor Agent is designed to translate security data into strategic insights for CISOs to present in the boardroom.
- It generates data-backed plans, identifies critical gaps, and offers what-if analyses to help align security efforts with organizational goals.
- Exabeam Nova now includes six purpose-built agents to automate decisions, streamline investigations, and provide recommendations for improving security operations.
Read Full Article
7 Likes
Socprime
247

Image Credit: Socprime
SOC Prime and Anetac
- SOC Prime and Anetac have partnered to enhance identity security and combat enterprise threats by integrating Identity Vulnerability Management with AI-powered Detection Engineering and Automated Threat Hunting.
- The partnership offers continuous identity threat detection, prioritized protection across attack paths, adversary behavior mapping with MITRE Attack Flow, vertical-specific detection content, and automated response and remediation workflows.
- By combining SOC Prime's Threat Detection Marketplace and Uncoder AI with Anetac's Identity Vulnerability Management Platform, the alliance aims to provide organizations with proactive, identity-focused threat-informed defense.
- The partnership's goal is to help security teams prioritize critical identity risks, enhance breach prevention, and improve overall cyber protection for both human and non-human identities across hybrid environments.
Read Full Article
14 Likes
Siliconangle
243

Image Credit: Siliconangle
LevelBlue to acquire Trustwave in push to expand managed cybersecurity capabilities
- LevelBlue Inc. has entered into an agreement to acquire Trustwave Holdings Inc., a managed detection and response company, for an undisclosed amount.
- Trustwave, known for its suite of cybersecurity services, will merge its capabilities with LevelBlue's strategic risk management and cybersecurity infrastructure.
- The acquisition will allow LevelBlue to leverage Trustwave's Fusion Platform for enhanced cloud-native MDR services and to meet U.S. government security standards like FedRAMP.
- The deal is set to strengthen LevelBlue's position in the cybersecurity market and will also involve strategic input from the Chertoff Group for further growth in the MDR segment.
Read Full Article
14 Likes
Siliconangle
4

Image Credit: Siliconangle
Concentric AI buys startups Swift Security and Acante to expand scope of data protection platform
- Concentric AI acquires Swift Security and Acante to enhance data protection platform.
- Acquisitions bring data loss prevention, generative AI governance tools to Concentric AI.
- Funding of $45 million in Series B enables Concentric to expand security offerings.
- Swift Security adds monitoring for unsafe use of generative AI tools; Acante assists in data access.
Read Full Article
Like
Securityaffairs
411

Image Credit: Securityaffairs
GDPR violations prompt Germany to push Google and Apple to ban DeepSeek AI
- Germany requested Google and Apple to remove DeepSeek AI from their app stores due to GDPR violations related to unlawful data collection and transfers to China.
- Berlin's Commissioner for Data Protection cited DeepSeek AI for processing extensive personal data of users, including chats and files, and transferring it to servers in China without adequate data protection measures.
- The Berlin Commissioner used the Digital Services Act to report DeepSeek AI to Apple and Google after the company failed to comply with requests to address GDPR violations. This was done in coordination with state data protection officers and the Federal Network Agency.
- Due to concerns over lack of EU safeguards and adequacy decisions for data transfers to China, DeepSeek AI has faced scrutiny from European authorities for violating GDPR standards, leading to calls for its removal from app stores.
Read Full Article
24 Likes
Hackernoon
310
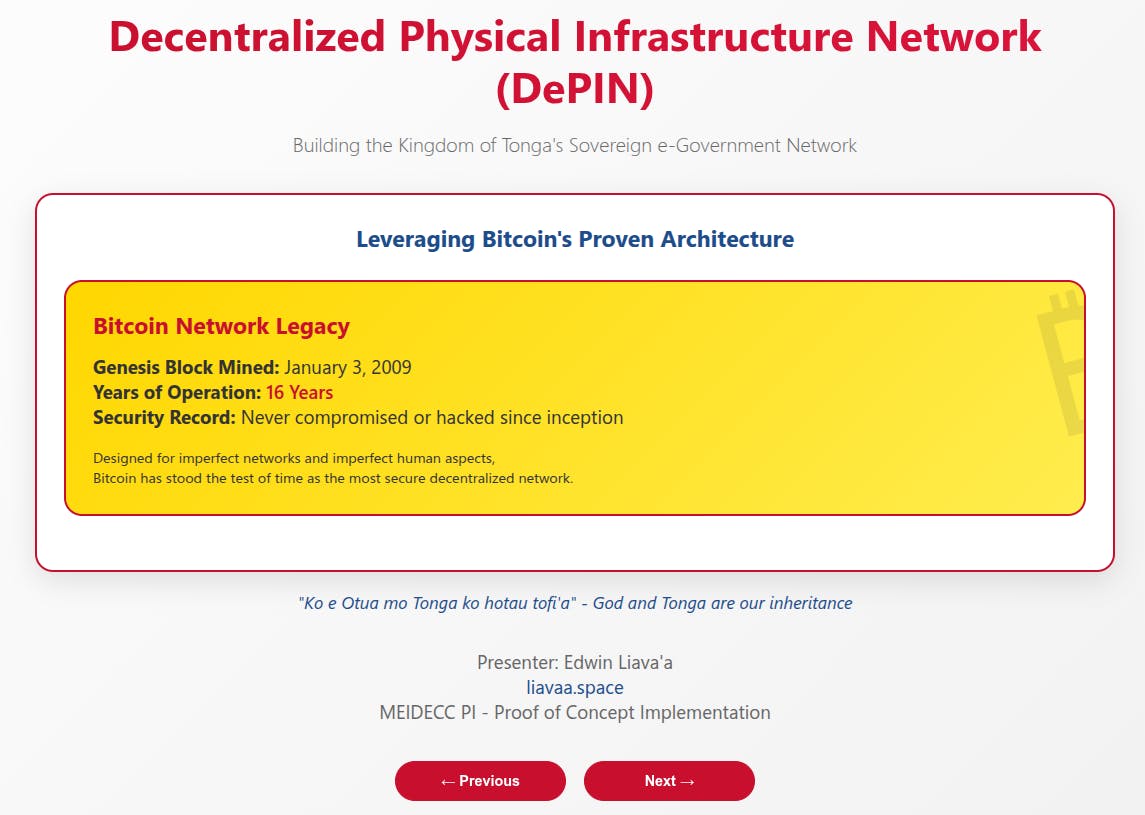
Image Credit: Hackernoon
From Crisis to Security - How DePIN Can Solve Tonga's Cybersecurity Challenges
- Recent data breaches in Tonga highlight critical vulnerabilities in current digital infrastructure.
- DePIN proposes a decentralized, blockchain-based system for secure government networks in Tonga.
- The solution aims for complete digital sovereignty and protection against cyber threats.
- DePIN's roadmap includes building secure infrastructure, network expansion, and economic benefits.
- The initiative envisions Tonga as a leader in digital independence and security.
Read Full Article
18 Likes
Dev
8

Image Credit: Dev
Promptfoo vs Deepteam vs PyRIT vs Garak: The Ultimate Red Teaming Showdown for LLMs
- Red teaming tools like Promptfoo, DeepTeam, PyRIT, and Garak are crucial for system safety.
- Promptfoo tailors test cases to your system, DeepTeam is fast with common vulnerabilities.
- PyRIT offers flexibility for complex red teaming, while Garak focuses on known issues.
- Each tool has its strengths and usage scenarios to ensure system resilience.
Read Full Article
Like
Global Fintech Series
0

Image Credit: Global Fintech Series
From Reactive to Resilient: 3 Practices to Help Financial Firms Thrive Amid Regulatory Change
- Navigating the changing regulatory landscape in financial services can be like a challenging game.
- Adapting to regulatory changes through embedding compliance in operations and balancing efficiency is key.
- Utilizing strategic partnerships for scalable expertise and proactive monitoring can help firms thrive.
Read Full Article
Like
Securityaffairs
92

Image Credit: Securityaffairs
Europol dismantles €460M crypto scam targeting 5,000 victims worldwide
- Europol dismantled a cryptocurrency fraud ring that scammed over 5,000 victims worldwide, laundering €460 million.
- The operation, named Operation Borrelli, was led by Spain's Guardia Civil and involved collaboration with law enforcement in Estonia, France, and the U.S.
- The scammers targeted victims through crypto romance scams on chats or dating apps, stealing money through fake platforms and using complex transfers to hide it.
- Five members of the criminal network were arrested, and authorities performed searches between the Canary Islands and Madrid to curb the cryptocurrency investment fraud.
Read Full Article
5 Likes
The Verge
227

Image Credit: The Verge
Tinder’s mandatory facial recognition check comes to the US
- Tinder is testing mandatory facial recognition security features in the US to verify profiles and combat fake accounts.
- New users in California must undergo a biometric 'Face Check' scan to confirm their identity, preventing impersonation and catfishing.
- The Face Check scan ensures that a user's face matches their profile photos and can detect duplicate accounts using the same face.
- The Face Check feature has been previously tested in Colombia and Canada with positive results, and Tinder will assess its reception in California before potentially expanding it nationwide.
Read Full Article
13 Likes
TechJuice
16

Image Credit: TechJuice
Hackers Are Now Deploying Stealthy Remcos Malware via Windows
- Hackers are deploying a stealthy Remcos Malware through PIF files, evading detection by antivirus software.
- Remcos Malware infiltrates systems, logging keystrokes, intercepting screenshots, delivering payloads, and maintaining persistence.
- It spreads through phishing emails and social media, tricking users with disguised files.
- Countermeasures include disabling PIF file execution, updating security tools, educating users, and monitoring endpoints.
Read Full Article
1 Like
For uninterrupted reading, download the app