Malware News
TechBullion
151

Image Credit: TechBullion
SpyCloud Pioneers the Shift to Holistic Identity Threat Protection to Counter Cyber Cybercriminals’ Evolving Tactics
- SpyCloud, a leading identity threat protection company, announced key innovations in its portfolio, pioneering the shift to holistic identity threat protection.
- By operationalizing its vast collection of darknet data with automated identity analytics, SpyCloud enables security teams to uncover hidden identity assets, rapidly remediate exposures, and better protect businesses from previously unseen threats.
- Their holistic identity threat protection addresses challenges by encompassing the full spectrum of an individual's online presence, proactively protecting against previously unseen risks.
- SpyCloud offers refined analytics, automated remediation, malware reverse engineering, and accelerated cybercrime investigations, empowering security teams to neutralize threats quickly and efficiently.
Read Full Article
9 Likes
Securityaffairs
380
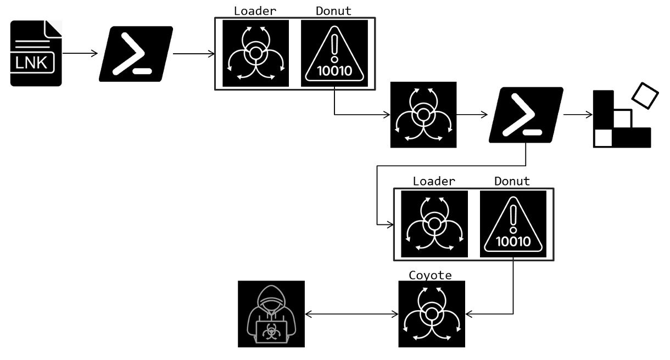
Image Credit: Securityaffairs
Coyote Banking Trojan targets Brazilian users, stealing data from 70+ financial apps and websites
- Coyote Banking Trojan targets Brazilian users, stealing data from over 70 financial applications and websites.
- Threat actors use LNK files and PowerShell commands to deploy the Coyote Banking Trojan.
- The Trojan supports keylogging, capturing screenshots, and displaying phishing overlays.
- The malware expands its targets to include 1,030 sites and 73 financial agents, posing a significant threat.
Read Full Article
22 Likes
Cybersecurity-Insiders
44

Image Credit: Cybersecurity-Insiders
WhatsApp users targeted by Paragon Spyware
- WhatsApp users targeted by Paragon Spyware.
- At least 90 individuals from over 50 countries were targeted by the Graphite spyware developed by Paragon.
- WhatsApp has sent a 'Cease and Desist' letter to Paragon, warning of legal consequences for engaging in unlawful cyber activities.
- Paragon may face similar outcomes as NSO Group, including losing contracts if the issue escalates.
Read Full Article
2 Likes
Medium
210

Image Credit: Medium
EDR Evasion Silencing Windows Event Generation
- Silencing Windows Event Logger functions is a powerful technique for bypassing EDR systems and reducing detection risk.
- By patching functions like EtwEventWrite, malware developers can disable event generation, neutralizing the mechanism used to monitor and flag suspicious activity.
- The provided code offers a step-by-step implementation to manipulate a target process's memory and silence the Windows Event Logger functions.
- While these methods showcase advanced evasion techniques, they emphasize the need for robust defensive strategies in cybersecurity.
Read Full Article
12 Likes
Securityaffairs
201
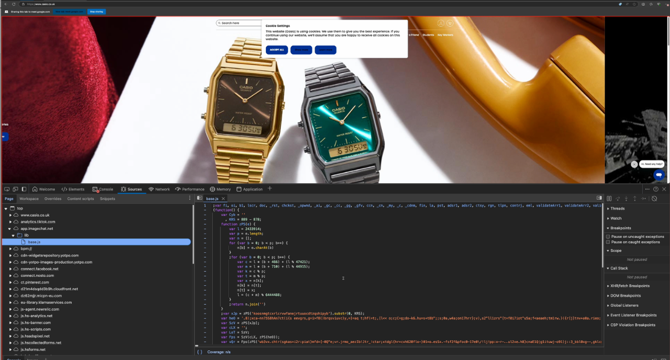
Image Credit: Securityaffairs
Web Skimmer found on at least 17 websites, including Casio UK
- A web skimmer has been discovered on the Casio UK website, as well as at least 17 other victim sites.
- The skimmer was placed on all pages of the Casio UK website, except the checkout page.
- The skimmer intercepted checkout clicks and displayed a fake payment form to steal users' personal details.
- The skimmer encrypted the stolen data using AES-256-CBC and sent it to a server controlled by the attackers.
Read Full Article
12 Likes
Sentinelone
123

Image Credit: Sentinelone
macOS FlexibleFerret | Further Variants of DPRK Malware Family Unearthed
- Apple has pushed an update, designed to combat variations of the macOS Ferret malware family, to its malware tool, XProtect.
- The family has been associated with the North Korean Contagious Interview campaign.
- Researchers have now found that the malware also uses Dropbox for exfiltration and api.ipify.org to resolve the host's public IP.
- A new set of malware samples called "FlexibleFerret" are currently not detected by XProtect.
- The name of the malware is related to the previous Ferret malware type.
- This particular malware variation masquerades as a legitimate Apple Developer installer package named vs.pkg and contains two applications InstallerAlert.app and versus.app.
- The malware's primary function is, while tricking the user into thinking it is a legitimate application, it installs a persistence item in the User's Library LaunchAgents folder with the label com.zoom.plist.
- Signatures in the malware are a functional match for the ChromeUpdate and shows 86% similarity to the previous Ferret malware variation.
- The 'Contagious Interview' campaign and Ferret malware remains an active and ongoing campaign.
- Finally, SentinelOne customers are protected from all known variants of the Ferret malware family
Read Full Article
7 Likes
Securityaffairs
137
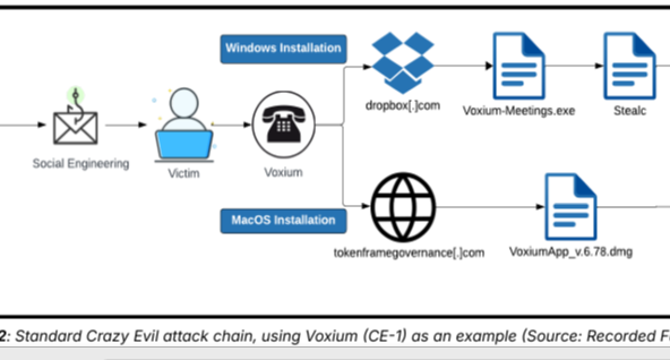
Image Credit: Securityaffairs
Crazy Evil gang runs over 10 highly specialized social media scams
- The Russian-speaking Crazy Evil group runs over 10 social media scams, tricking victims into installing StealC, AMOS, and Angel Drainer malware.
- The group's subteams target specific victim profiles, using phishing, identity fraud, and malware to steal cryptocurrency.
- Crazy Evil has earned over $5 million through phishing scams since 2021, targeting high-value victims in the cryptocurrency space.
- The group maintains a strong presence on dark web forums, collaborates with other cybercrime gangs, and focuses on targeting the Web3 and decentralized finance sector.
Read Full Article
8 Likes
Kaspersky
151

Image Credit: Kaspersky
New Tria stealer intercepts text messages on Android | Kaspersky official blog
- Cybercriminals are using WhatsApp with APK attachments disguised as wedding invitations to launch attacks on Android smartphone users in Malaysia and Brunei.
- Kaspersky's research revealed that malicious APKs were being circulated over WhatsApp.
- The scam uses two versions of the same stealer malware, which Kaspersky has dubbed Tria.
- The Tria malware harvests data from text and email messages, reading call logs and message logs to help attack victims' Telegram and WhatsApp accounts.
- The scams have so far been limited to Malaysia and Brunei and have not targeted specific individuals.
- The Tria stealer has added social engineering tactics to hide behind a gear icon, mimicking a system application to gain access to ten permissions, including access to network activity and the ability to send and read text messages.
- Kaspersky advises phone users to only use official app stores and developer websites when downloading apps, to be wary of anyone they do not know contacting them through messenger apps, and never to grant apps more permissions than they need.
- Kaspersky also recommends using an authenticator app to generate 2FA codes and setting up a Telegram cloud password.
- In addition, users can download Kaspersky for Android to protect themselves against Tria and other potential attacks.
- If Tria malware gains access to online banking accounts, it can request and intercept OTP codes needed for login.
Read Full Article
9 Likes
Securityaffairs
284

Image Credit: Securityaffairs
Security Affairs newsletter Round 509 by Pierluigi Paganini – INTERNATIONAL EDITION
- A ransomware attack forced New York Blood Center to reschedule appointments
- Contec CMS8000 patient monitors contain a hidden backdoor
- Community Health Center data breach impacted over 1 million patients
- Italy’s data protection authority Garante blocked the DeepSeek AI platform
Read Full Article
17 Likes
Securityaffairs
421

Image Credit: Securityaffairs
WhatsApp disrupted a hacking campaign targeting journalists with Paragon spyware
- WhatsApp disrupted a hacking campaign targeting journalists with Paragon spyware.
- Meta discovered and dismantled a malware campaign via WhatsApp that targeted journalists and civil society members with the Paragon spyware.
- The hacking campaign targeted 90 users and was disrupted in December.
- WhatsApp linked the hacking campaign to Paragon, an Israeli commercial surveillance vendor.
Read Full Article
25 Likes
Securityaffairs
316

Image Credit: Securityaffairs
Ransomware attack hit Indian multinational Tata Technologies
- Indian multinational Tata Technologies, a Tata Motors subsidiary, suspended some IT services following a ransomware attack.
- The company confirmed that the ransomware attack has impacted a limited part of its IT infrastructure.
- Tata Technologies temporarily suspended some of its IT services as a precautionary measure.
- Client delivery services of the company were not affected by the attack.
Read Full Article
19 Likes
Securityaffairs
385

Image Credit: Securityaffairs
A ransomware attack forced New York Blood Center to reschedule appointments
- The New York Blood Center faced a ransomware attack on Sunday, forcing the healthcare organization to reschedule appointments.
- NYBC and its operating divisions provide transfusion-related medical services and supply blood to approximately 200 hospitals in the Northeast United States.
- The ransomware attack was discovered on January 29, and the organization immediately took steps to mitigate and contain the attack.
- NYBC is working with cybersecurity experts to restore the impacted systems and there is no set timeline for system restoration.
Read Full Article
23 Likes
Kaspersky
280
Image Credit: Kaspersky
Ransomware attacks in 2024 | Kaspersky official blog
- Ransomware attacks continued to proliferate in 2024, and Kaspersky presents several of the most impactful incidents. These incidents include the following:
- Toronto Zoo ransomware attack: Attackers stole large amounts of personal information from zoo employees.
- UnitedHealth ransomware attack: Attackers demanded a $22 million ransom while stealing $3.09 billion worth of data, including medical data of more than 100 million U.S. residents.
- Panera Bread ransomware attack: Personal data of employees was stolen, and the company paid a ransom.
- Hoya Corporation ransomware attack: Attackers stole 1.7 million files and demanded $10 million.
- Ascension ransomware attack: The personal data of 5.6 million patients and hospital staff was stolen.
- Synnovis ransomware attack: The attack led to over 800 canceled surgeries and a shortage of blood in hospitals.
- Los Angeles County Superior Court ransomware attack: All 36 courthouses in the county were shut down due to the attack.
- Stoli Group ransomware attack: ERP system failure led to all internal processes being transferred to manual mode and the eventual bankruptcy of the company.
- Highline Public Schools ransomware attack: All 34 schools had to close temporarily, and the company paid for credit monitoring services for staff.
Read Full Article
16 Likes
Socprime
330

Image Credit: Socprime
Lumma Stealer Detection: Sophisticated Campaign Using GitHub Infrastructure to Spread SectopRAT, Vidar, Cobeacon, and Other Types of Malware
- Lumma Stealer, along with other malware variants, is being distributed through the GitHub infrastructure in a sophisticated campaign.
- Lumma Stealer is a data-stealing malware that extracts credentials and files while connecting to adversary servers.
- Defenders can use SOC Prime Platform to access detection content and Sigma rules for Lumma Stealer and other associated malware.
- To mitigate threats like Lumma Stealer, organizations are advised to validate URLs and files, inspect email attachments, and enforce a zero-trust approach.
Read Full Article
19 Likes
Cybersecurity-Insiders
409

Image Credit: Cybersecurity-Insiders
Ransomware attack makes Tata Technologies suspend whole of its IT services
- Tata Technologies suspended its IT services as a precautionary measure against a ransomware attack.
- All suspended services were restored within 3 hours, minimizing downtime.
- Ransomware attacks involve hackers encrypting data and demanding a ransom.
- Law enforcement advises against paying ransom as there is no guarantee of receiving decryption key.
Read Full Article
24 Likes
For uninterrupted reading, download the app