Hacking News
Hackers-Arise
106

Image Credit: Hackers-Arise
Windows Network Exploitation with Impacket Framework
- Impacket is a Python library that provides low-level access to network protocols essential for network protocol exploitation and lateral movement in hacking/penetration testing.
- It implements Windows protocols like SMB, MSRPC, LDAP, and Kerberos, offering granular control over protocol communication.
- Impacket tools like psexec.py and wmiexec.py enable remote code execution on Windows systems using legitimate protocols, allowing blending with normal network traffic to evade detection.
- To install Impacket, one can clone from the GitHub repository, set it up in a Python virtual environment, and verify the installation.
- Usage examples such as running psexec.py for remote code execution, leveraging PSExec utility, and using various methods like PowerShell for evasion are discussed.
- Credential harvesting with tools like secretsdump.py, extraction of Windows credentials including password hashes and Kerberos tickets, and pass-the-hash authentication methods are highlighted.
- Additional evasion techniques, process name obfuscation, execution through different interpreters, and saving output to files for credentials are explored.
- Impacket offers various utilities for LDAP enumeration, Kerberos-based attacks, and Active Directory exploitation, making it a sophisticated penetration testing framework.
- Impacket is recommended as an essential tool for hackers due to its capabilities, with mastering the utilities providing access to advanced penetration testing functionalities.
- The post concludes by suggesting upgrading to a Member Gold subscription for access to a comprehensive library of advanced courses.
Read Full Article
6 Likes
Securityaffairs
44

Image Credit: Securityaffairs
Palo Alto Networks fixed multiple privilege escalation flaws
- Palo Alto Networks addressed multiple privilege escalation vulnerabilities and integrated the latest Chrome security patches into its products.
- The company fixed seven privilege escalation flaws and patched CVE-2025-4233, a cache vulnerability impacting the Prisma Access Browser.
- The most severe vulnerability, CVE-2025-4232, allows authenticated code injection through wildcard on macOS with a CVSS score of 7.1.
- A vulnerability in the log collection feature of GlobalProtect app on macOS allows non-admin users to escalate privileges to root.
- Palo Alto Networks also addressed a PAN-OS Authenticated Admin Command Injection Vulnerability (CVE-2025-4231) affecting the Management Web Interface.
- The company fixed a PAN-OS flaw (CVE-2025-4228) exposing unencrypted SD-WAN data and a Cortex XDR Broker VM bug allowing attackers to escalate privileges to root.
- Palo Alto Networks is not aware of any attacks exploiting these vulnerabilities in the wild.
Read Full Article
2 Likes
TheNewsCrypto
191

Binance Aids Philippines in Busting $3.75M Crypto Ransom Scheme
- Binance assisted Philippine law enforcement in dismantling a $3.75 million crypto ransom scheme.
- The collaboration allowed investigators to identify suspects and track illegal fund flows on the blockchain.
- The involvement of private junket operators complicated tracking transactions for the Anti-Cybercrime Group of the Philippine National Police.
- Binance disabled associated assets, disrupting the money laundering operation.
- The crypto exchange prevented over $3.5 million in US dollars related to the scheme.
- An individual named Lin was arrested in the US for various criminal activities.
- Binance's efforts have also assisted in uncovering cybercriminal networks in Thailand and Malaysia.
- Crypto currencies present challenges to global law enforcement, despite blockchain transparency aiding in identifying illicit finance.
- Bitcoin fell below $104K amidst tensions between Iran and Israel.
Read Full Article
11 Likes
Securityaffairs
4

Image Credit: Securityaffairs
Unusual toolset used in recent Fog Ransomware attack
- Fog ransomware operators used unusual pentesting and monitoring tools in a May 2025 attack on an Asian financial firm, as reported by Symantec researchers.
- The attackers utilized rare tools like Syteca monitoring software, GC2, Adaptix, and Stowaway, which are uncommon in ransomware campaigns.
- After the attack, the attackers established a service for maintaining access, demonstrating a rare persistence move, and remained undetected in the network for two weeks before deploying the ransomware.
- Fog ransomware has been active since at least May 2024, initially targeting U.S. schools through compromised VPNs and later exploiting a Veeam VBR vulnerability.
- In April 2025, the attackers shifted to email-based infections, employing provocative tactics in ransom notes to infect victims and offering free decryption in exchange for infecting others.
- While the initial infection vector in the recent Fog ransomware attack remains unknown, experts suspect Exchange Servers may have played a role.
- The attackers' toolkit included uncommon tools like GC2 for C2 communication, Syteca for monitoring, Stowaway for delivery, and PsExec/SMBExec for lateral movement, indicating espionage motives.
- Additionally, tools like Adaptix C2, FreeFileSync, MegaSync, and Process Watchdog were used for data theft, maintaining persistence, and controlling the compromised network.
- The atypical toolset and post-deployment persistence in the attack suggest potential espionage motives of the attackers, using ransomware possibly as a decoy or secondary goal.
- The report highlights the possibility of the company being targeted for espionage, with ransomware serving as a diversion or profit-making tactic alongside espionage activities.
- The use of uncommon tools in the ransomware attack is a noteworthy observation for businesses seeking to defend against malicious actors, according to the researchers.
- Overall, the attack's unique characteristics and toolset underscore the need for enhanced cybersecurity measures and vigilance against sophisticated threat actors.
- The presence of indicators of compromise in the report provides valuable insights for organizations to bolster their defenses.
- Follow @securityaffairs on Twitter, Facebook, and Mastodon for related updates and news.
- The article was authored by Pierluigi Paganini and covers details on the hacking incident involving Fog ransomware.
- SecurityAffairs reports on hacking incidents and cybersecurity matters related to Fog ransomware.
Read Full Article
Like
Securityaffairs
146

Image Credit: Securityaffairs
A cyberattack on United Natural Foods caused bread shortages and bare shelves
- United Natural Foods Inc. (UNFI) was hit by a cyberattack on June 5, causing disruptions in deliveries and shortages at Whole Foods stores nationwide.
- The cyberattack affected UNFI's ability to fulfill and distribute customer orders, causing temporary disruptions to its operations.
- Details about the attack were not disclosed by United Natural Foods, but similar incidents in the past have been linked to ransomware attacks.
- Whole Foods stores experienced significant shortages, with shelves left bare and inadequate shipments due to communication issues with UNFI.
- Employees from various Whole Foods locations reported bread and supply shortages as a result of the cyberattack.
- UNFI has begun the process of restoring systems, but a clear recovery timeline has not been provided.
- The cyberattack's impact extended beyond Whole Foods, affecting smaller retailers like the Community Food Co-Op in Bellingham, Washington.
- The Community Food Co-Op notified customers about sparse shelves and requested limiting purchases to ensure access to essential items during the recovery phase.
Read Full Article
8 Likes
Hackers-Arise
226

Image Credit: Hackers-Arise
Web App Hacking: Katana, A Next-Generation Crawling and Spidering Framework
- Katana is a next-generation crawling and spidering framework developed by security researchers at ProjectDiscovery.
- It offers advanced capabilities to map, crawl, and spider modern, complex web applications effectively.
- Katana excels in handling JavaScript execution and dynamic content rendering, unlike traditional crawling tools.
- It supports two main crawling modes: Standard Mode for speed and simplicity, and Headless Mode for comprehensive crawling of JavaScript-heavy applications.
- Katana can be installed using the Go programming language, providing users with different installation methods.
- The framework allows for basic website reconnaissance and crawling of JavaScript-heavy applications like AngularJS-based sites.
- Users can leverage Katana to discover known files like robots.txt and sitemap.xml, revealing valuable insights into website structures.
- The tool offers filtering capabilities to isolate valuable data during crawls, enabling users to focus on specific goals and reduce noise.
- Katana's flexibility in filtering output data by fields, extensions, and regex patterns enhances user precision in handling crawl results.
- Overall, Katana is a powerful tool for penetration testing, bug bounty research, and cybersecurity operations with its modern architecture and advanced features.
Read Full Article
13 Likes
Hackers-Arise
253

Image Credit: Hackers-Arise
VPN Hacking: How VPN’s Work and How They Break Our Security
- VPN's, both consumer-level and corporate-level, are designed to encrypt data and provide secure network connections.
- Consumer-level VPN's hide IP addresses and encrypt data, but may not fully protect user identities against newer tracking methods like cookies and browser fingerprinting.
- Corporate-level VPN's enable remote employees to securely access the company network but have vulnerabilities, especially in server security which, if breached, can compromise all VPN traffic.
- Studies show a significant increase in VPN vulnerabilities, with 91% of companies concerned about VPN risks and 56% being targeted in cyberattacks.
- Multiple major VPN vendors have been identified with critical vulnerabilities exposing users to risks such as OS command injections, memory corruption, privilege escalation, and arbitrary code execution.
- Other vulnerabilities include buffer overflows, memory safety vulnerabilities, cleartext storage of sensitive data, improper verification, denial of service attacks, and more.
- Exploiting these vulnerabilities could lead to serious consequences, including data breaches, remote code execution, privilege escalation, DoS attacks, and unauthorized access.
- Due to these widespread vulnerabilities, it is crucial for VPN users and providers to stay vigilant, apply patches promptly, and adopt robust security measures to mitigate potential risks.
Read Full Article
15 Likes
Hackers-Arise
271

Image Credit: Hackers-Arise
VPN Vulnerabilities You Should Know About in 2025
- VPNs are facing increasing vulnerabilities in both consumer and corporate settings, with hackers exploiting weaknesses regularly.
- In April 2025, CVE-2025-22457, a critical stack-based buffer overflow vulnerability, was identified in Ivanti Connect Secure and Pulse Connect Secure VPN appliances.
- This vulnerability was previously considered non-exploitable but was discovered to be weaponizable by a Chinese APT group.
- CVE-2024-53704 is an authentication bypass vulnerability in SonicWall SSL VPN, allowing remote attackers to hijack active VPN sessions.
- Ivanti disclosed CVE-2025-0282 and CVE-2025-0283, critical stack-based buffer overflows enabling remote code execution and local privilege escalation.
- A DoS vulnerability (CVE-2025-20212) affecting Cisco Meraki AnyConnect VPN servers requires valid user credentials to exploit.
- X41 D-Sec GmbH found a critical vulnerability (CVE-2024-55884) in the Mullvad VPN application, leading to memory corruption and out-of-bounds writes.
- The identified vulnerabilities highlight the ongoing risks associated with VPNs, making them attractive targets for cyber threats.
- A VPN hacking training is scheduled for June 2025 to address these emerging threats.
Read Full Article
16 Likes
Securityaffairs
218

Image Credit: Securityaffairs
Paraguay Suffered Data Breach: 7.4 Million Citizen Records Leaked on Dark Web
- Resecurity researchers discovered 7.4 million records of Paraguay citizens' personally identifiable information (PII) on the dark web, with cybercriminals demanding $7.4 million in ransom payments.
- The stolen data was offered for sale, with a symbolic deadline set by a ransomware group.
- The leaked data includes PII from different government systems, accusing the country's leadership of corruption and lack of data protection.
- The Paraguayan government refused to pay the ransom and did not provide details on how the data of 7.5 million citizens was compromised.
- The leak is suspected to be from various government institutions, including the National Agency for Transit and Road Safety and the Ministry of Public Health and Social Welfare.
- Past data breaches in Paraguay were noted, including incidents in 2025 involving over 7 million people and sensitive data from public institutions.
- The cybercriminals referred to themselves as 'Cyber PMC' and targeted government systems for profit, raising concerns about potential foreign state involvement.
- The growing number of cyberattacks against Paraguay, possibly linked to Chinese state-sponsored groups like Flax Typhoon, is highlighted.
- No data was leaked in the Flax Typhoon incident, which employed advanced persistent threats to infiltrate systems.
- Paraguay's stance on Taiwan's independence has led to heightened cyber threats, with foreign actors targeting government systems storing citizen PII.
- The trend of increasing cyber threats in South America underscores the need for greater vigilance in safeguarding government information systems and citizen data.
- Flax Typhoon, a cyber-group linked to China, conducted an advanced persistent threat (APT) attack on Paraguayan government networks.
- The Paraguayan government has taken steps to address the cyber threats and emphasized the importance of protecting sensitive information.
- The significant data breach in Paraguay involving 7.4 million citizens signifies a critical cybersecurity incident in the nation's history.
- This incident raises concerns about the vulnerability of government systems and the need for robust cybersecurity measures to safeguard citizen data.
- The extensive scope of the data breach, previous incidents, and potential foreign involvement underscore the urgency for enhanced cybersecurity protocols in Paraguay.
Read Full Article
13 Likes
Securityaffairs
48

Image Credit: Securityaffairs
Apple confirmed that Messages app flaw was actively exploited in the wild
- Apple confirmed that a security flaw in its Messages app, CVE-2025-43200, was actively exploited in the wild targeting journalists with Paragon’s Graphite spyware.
- The vulnerability was addressed on February 10, 2025, with the release of multiple updates including iOS 18.3.1 and macOS versions.
- The flaw allowed a logic issue when processing a maliciously crafted photo or video shared via an iCloud Link.
- Citizen Lab confirmed Graphite spyware was used to hack fully updated iPhones, targeting journalists in Europe.
- Forensic evidence showed communication with the same spyware server. Apple alerted victims and patched the zero-click exploit.
- Paragon accused the Italian government of refusing help to investigate spyware use against a journalist, leading to ending contracts in Italy.
Read Full Article
2 Likes
Securityaffairs
31

Image Credit: Securityaffairs
Trend Micro fixes critical bugs in Apex Central and TMEE PolicyServer
- Trend Micro addressed critical vulnerabilities in its Apex Central and Endpoint Encryption PolicyServer products.
- The vulnerabilities impact products such as Trend Micro Endpoint Encryption (TMEE) PolicyServer and Apex Central.
- Apex Central is a centralized management server used in Trend Micro’s Endpoint Encryption solution.
- A patch has been released to resolve several vulnerabilities in Trend Micro Endpoint Encryption PolicyServer.
- The vulnerabilities include SQL injection privilege escalation, deserialization RCE, and authentication bypass issues.
- Trend Micro highlighted the need for immediate application of security updates to mitigate risks.
- No evidence of active exploitation has been reported for these vulnerabilities.
- The company fixed flaws in Apex Central related to deserialization RCE vulnerabilities.
- The vulnerabilities in Apex Central have not been actively exploited in the wild.
- Administrators use Apex Central for centralized management of Trend Micro products and services.
- Apex Central provides a single monitoring point for network-wide antivirus and content security products.
- Follow @securityaffairs, @Facebook, @Mastodon for more cybersecurity news.
- Author: Pierluigi Paganini (SecurityAffairs - hacking, Apex Central)
Read Full Article
1 Like
TechCrunch
240

Image Credit: TechCrunch
Apple fixes new iPhone zero-day bug used in Paragon spyware hacks
- Apple has fixed a zero-day bug that was used by the Paragon spyware to hack iPhones of two European journalists.
- The Citizen Lab report mentioned that the flaw was mitigated in iOS 18.3.1 that was released on February 10.
- The security update initially only addressed an unrelated flaw, but was later updated to include details about a logic issue in processing media via an iCloud Link.
- The flaw was exploited in an attack against specific individuals, including Italian journalist Ciro Pellegrino and another European journalist.
- Apple did not disclose the existence of this patched flaw until four months after the iOS update release.
- The Paragon spyware scandal started in January with WhatsApp notifying users of being targeted with Graphite spyware.
- Several iPhone users later received notifications from Apple about being targets of mercenary spyware.
- The Citizen Lab's findings confirmed that two journalists targeted with Apple's notification were hacked with Paragon spyware.
- It's uncertain if all Apple users who received the notification were targeted with Graphite.
- Apple did not provide a comment on the reason for the delayed disclosure of the patched flaw.
- The report mentions users in 100 countries received notifications about being affected by the spyware campaign.
Read Full Article
14 Likes
Securityaffairs
405

Image Credit: Securityaffairs
SinoTrack GPS device flaws allow remote vehicle control and location tracking
- U.S. CISA warns of two vulnerabilities in SinoTrack GPS devices enabling remote vehicle control and location tracking by attackers.
- Potential exploitation could allow attackers to track the vehicle's location or cut power to the fuel pump.
- CVE-2025-5484 involves a default password shared across all SinoTrack units, making unauthorized access easy.
- CVE-2025-5485, similar to CVE-2025-5484, involves a default password shared across devices.
- CISA advises changing default passwords, hiding device IDs, and assessing risks before taking action.
- Users are recommended to contact the vendor directly as SinoTrack did not respond to CISA's warnings.
- CISA suggests following cybersecurity best practices, avoiding phishing links, and reporting suspicious activity.
- No known public exploitation of the vulnerabilities has been reported.
- Users should remain vigilant and prioritize security measures to protect their devices and data.
- The vulnerabilities underscore the importance of securing IoT devices against potential cyber threats.
- Experts highlight the need for manufacturers to prioritize robust security measures in IoT devices.
- The SinoTrack GPS vulnerabilities serve as a reminder of the risks associated with default passwords and lack of security controls.
- It is crucial for users to proactively secure their IoT devices to prevent unauthorized access and potential misuse.
- CISA's advisory aims to raise awareness about the vulnerabilities in SinoTrack GPS devices and promote preventative actions.
- The security community emphasizes the significance of addressing vulnerabilities promptly to safeguard users' privacy and safety.
- The advisory serves as a call to action for users to take proactive steps in securing their IoT devices.
- Clarifications and updates may be necessary as the situation evolves, and further responses are awaited from SinoTrack regarding these critical vulnerabilities.
Read Full Article
24 Likes
Siliconangle
218

Image Credit: Siliconangle
Cloudflare sees massive rise in attacks targeting media, nonprofits and human rights groups
- Cloudflare's report on cyberattacks targeting civil society organizations reveals a surge in attacks, with application-layer DDoS attacks surpassing web exploit attempts.
- Project Galileo by Cloudflare provides free cybersecurity protection to at-risk organizations like media, nonprofits, and human rights groups to defend against cyber threats.
- In the period up to March 31, Cloudflare blocked 108.9 billion threats targeted at Galileo-protected entities, marking a 241% increase from the previous year.
- Independent media and journalists were the most targeted groups, facing over 97 billion blocked requests, followed by civil society and human rights organizations with nearly 9 billion requests.
- Environmental and disaster relief groups experienced over 1 billion malicious requests, posing risks to critical emergency updates and operations.
- Social welfare organizations, including healthcare providers, were hit with 1.5 billion attacks, with one incident impacting a Polish healthcare charity just before a major fundraiser.
- Complex, multi-day attacks were observed, as seen in a 12-day campaign against Tech4Peace, demonstrating strategies to test and bypass defenses.
- Cloudflare also detected coordinated attacks on Ukrainian public safety websites during Russian drone strikes, possibly aiming to disrupt real-time alert systems.
- The report underlines the vulnerability of human rights groups to cyber threats due to limited resources for strong cybersecurity defenses, emphasizing the need to protect these organizations.
Read Full Article
13 Likes
Securityaffairs
338
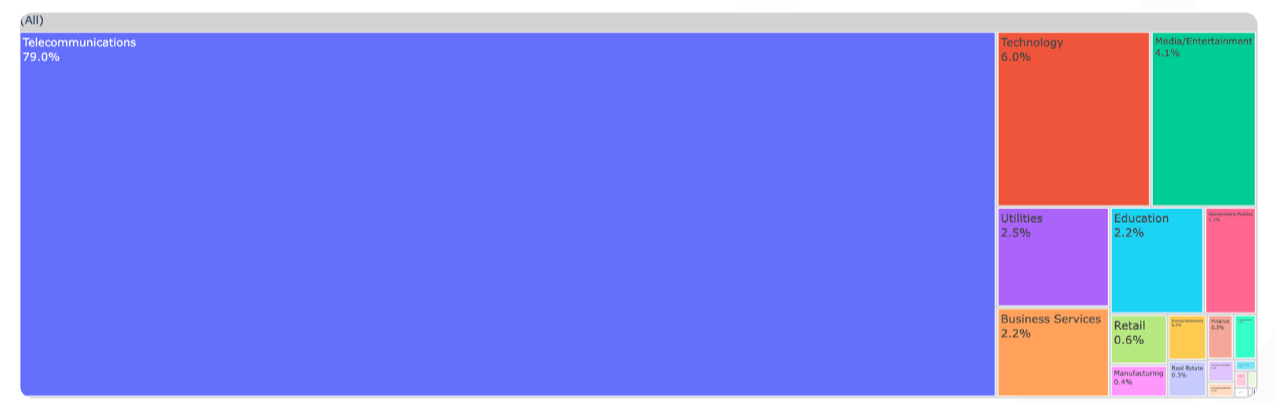
Image Credit: Securityaffairs
Exposed eyes: 40,000 security cameras vulnerable to remote hacking
- Over 40,000 internet-exposed security cameras worldwide are vulnerable to remote hacking, posing serious privacy and security risks.
- Bitsight alerts about the vulnerability of security cameras to remote hacking due to unsecured HTTP or RTSP access, enabling live feed streaming that can be easily targeted for spying, cyberattacks, and stalking.
- Identification of HTTP-based security cameras is complex due to diverse models; researchers developed a fingerprinting method using favicon hashes, HTTP headers, and HTML titles.
- Many HTTP-based cameras allow unauthenticated access to live footage through specific URIs like /out.jpg, which poses a significant privacy risk by bypassing authentication.
- RTSP-based cameras lack clear identifiers, making them harder to fingerprint; researchers analyzed RTSP Server headers and common URIs like /live.sdp to capture screenshots.
- Bitsight's internet scan revealed over 40,000 exposed cameras, mainly in the U.S., with the Telecommunications sector having the highest exposure due to extensive consumer use.
- The risk of privacy breaches and security threats extends to various sectors, including technology, media, utilities, business services, and education, as poorly secured cameras provide access to sensitive areas.
- Exposed cameras can capture live footage from homes, offices, retail spaces, factories, and critical areas, enabling spying, robbery planning, and data theft due to insecure setups.
- Bitsight warns of cybercriminals searching for exposed cameras on dark web forums and recommends users to update devices, change default passwords, disable unnecessary remote access, secure connections, and monitor unusual logins.
- The report underlines the significant exposure of devices in the Telecommunications sector, emphasizing the widespread availability of cameras for personal and professional use.
Read Full Article
20 Likes
For uninterrupted reading, download the app